
The integral role that language plays in insurance services has been emphasised by the COVID crisis as the consequences of ambiguous policy wordings have reverberated across the insurance sphere. It’s a message that the Geneva Association has been addressing for years, particularly in the cyber space, where the (re)insurance community would benefit from common language to define cyber events and a common approach to incident attribution.
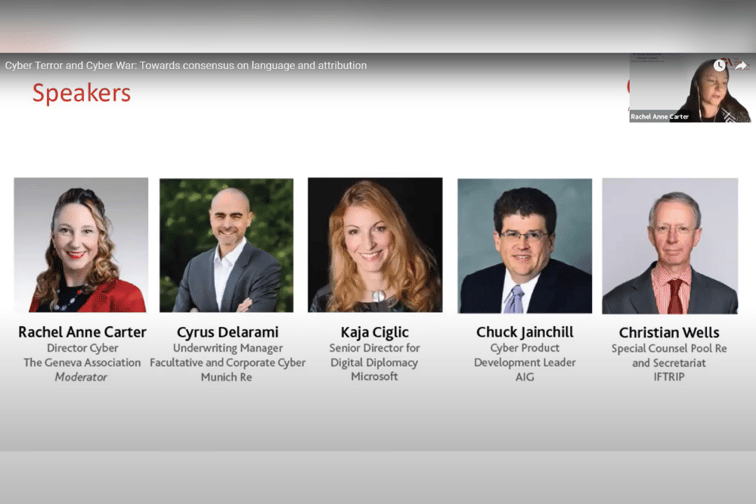
The Geneva Association deliberated this question of attribution during its latest #RiskConversations webinar, where its director of cyber, Rachel Anne Carter, moderated a panel discussion featuring several senior industry leaders. One question posed to the panel, which included representatives from Microsoft, Munich Re and IFTRIP, among others, examined whether government buy-in is required when it comes to the attribution of cyber events.
Christian Wells, special counsel, Pool Re and secretariat, IFTRIP, highlighted that, while government involvement undoubtedly helps with attribution in the sense of providing an answer, it doesn’t necessarily provide a wholly accurate answer, even where there is an agreed process. A lot of national pools around the world don’t actually have formal processes, he said, they merely have contact with their governments.
“In the case of Pool Re,” he said, “we have a formal process for the certification of an event but it’s a bit like a black box - we submit a request for certification to the government who will then issue a certification that something is or isn’t, in the case of Pool Re, an act of terrorism. So, there may be a number of factors at play on whether a government certifies something as terrorism or as hostile cyber activity or otherwise. It’s an easier approach, not necessarily a failsafe one.”
Offering his perspective, Chuck Jainchill, cyber product development leader at AIG noted that the best-case scenario is having some form of governmental or international way of certifying or determining attribution. But, as with all things relating to insurance policies, he said, attribution may have to be determined legally in court. And the standard in the US, and most places, for civil litigation hinges on factors such as a preponderance of the evidence.
Even though a state may not be willing to take the position that an adversary or a friend was the perpetrator of an event, he said, the court has the standard of expert testimony and a variety of sources. Public-private partnerships and government buy-in is the ideal - but in the absence of that, the insurance industry must establish how to determine where these events fall on the spectrum.
Offering a non-insurance view Kaja Ciglic, senior director for digital diplomacy at Microsoft, who has previously been involved with governments on this subject, stated that public attribution tends to be a political process. When governments call out other governments for malicious activity, there’s usually more at play than a specific activity.
“I will also say there’s often times we, as the public, don’t necessarily hear about it and attributions are made behind closed doors, which may not [be relevant] to this conversation, but is part of the political and international relations game, and might actually help the situation improve,” she said. “From the tech industry perspective, we at Microsoft and others tend to call out specific groups, rather than necessarily governments on their actions. The groups themselves might operate from a particular location, and we are able to call that out - but the link between a state and the particular group is difficult to establish.”
Indeed it is difficult even in normal international law, Ciglic said, but is even more complex in the cyber space. It’s this link that tends to be missing when the industry tackles attribution by itself and why government action, especially around signals intelligence, is both called for and relied on. She encouraged viewers to look closer at the Solar Winds attribution recently made by the US and noted that it was not just a timely occurrence but also one of the first she has seen take such a comprehensive overview. The detail that was published, both in terms of technical detail and normative law detail, was significant and should be encouraged as it will improve the situation of every stakeholder.
“Cyber insurance requires unique perspectives on the way we’re looking at the problems of terrorism and warfare,” Jainchill said. “And, among other things… cyber is international, it’s going across borders and it doesn’t discriminate where Britain ends or Europe starts... So, the need for international cooperation is probably larger here than other areas of insurance.”
