
This article was produced in partnership with Tokio Marine HCC – Cyber & Professional Lines Group.
Bethan Moorcraft of Insurance Business sat down with Alex Bovicelli, Director of Threat Intelligence in the Tokio Marine HCC – Cyber & Professional Lines Group to discuss cyber threat intelligence.
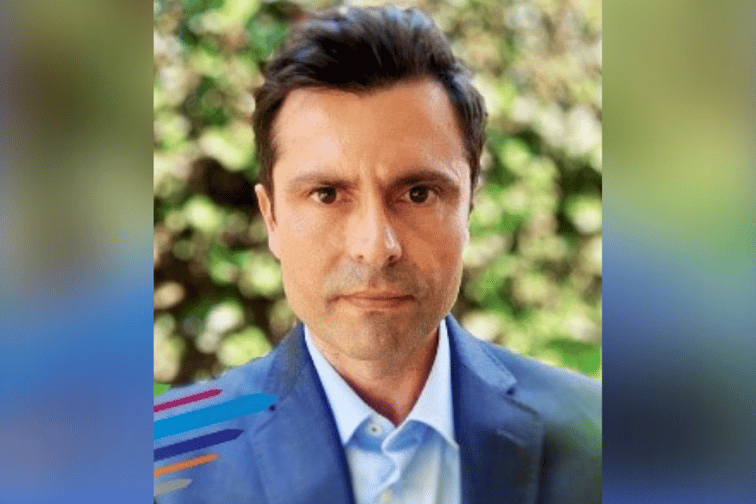
Tokio Marine HCC – Cyber & Professional Lines Group recently appointed Alex Bovicelli (pictured) as Director of Threat Intelligence, to be responsible for reducing exposure in the group’s cyber portfolio, aiding the risk assessment process and monitoring threat capabilities for its policyholders.
Bovicelli has extensive knowledge and expertise of the cyber threat landscape and is well-informed about the trends coming out of the complex criminal cyber-underworld. He joined Tokio Marine HCC – Cyber & Professional Lines Group from the University of Southern California, where he was the Lead Cyber Threat Intelligence Analyst and developed and implemented cyber threat intelligence programs and models in an effort to improve the institution’s cyber security posture.
“Cyber threat intelligence has been a ‘buzzword’ for a few years now,” according to Bovicelli. He explained that threat intelligence has one key aim, which is to reduce uncertainty, whether in a “technical security” function within a SOC (Security Operations Center) or to better inform business decisions with the aim of reducing budgetary risk and monetary loss.
“Simply put, a best-in-class cyber threat intelligence (CTI) program should provide a measurable advantage,” Bovicelli told Insurance Business. “It should function seamlessly while serving multiple groups. Due to cybersecurity and threat information that organizations have at their disposal, CTI should reduce risk to the organization it serves by identifying ‘what matters’ to that specific organization. This is true in whatever form it is applied.
“Most commonly, a CTI team will be imbedded in the SOC to provide technical indicators of threats that are likely to target an organization and leverage that knowledge in ‘threat hunting’ to discover undetected intrusions on the network. But it should follow a cyclical process, continuously realigning itself to forecast and counter possible risks to the organization.”
Read more: Tokio Marine HCC bolsters cyber practice
While it may sound very complex, CTI actually follows basic threat-modeling processes. Bovicelli described the practice as “a technical process driven by a non-technical method”. He explained: “It is driven by analysis and a continuous push to reassess and understand intelligence requirements, known as ‘knowledge gaps,’ that need to be filled in order to get ahead of the adversary. Because of this, intelligence can essentially be applied to any field or market, and does not have to rely on a specific set of tools or technology.”
Bovicelli gave the example of using CTI to learn from ransomware compromises – arguably an area of high-priority given the dramatic uptick in both the frequency and severity of ransomware attacks in the past 12-18 months. Analyzing ransomware attacks to understand how threat actors gain initial access into companies’ internal networks, and whether hackers exploited any specific vulnerabilities, is critical for assessing the likelihood and reducing the impact of future events.
“While CTI within security operations is understood as a defensive function that provides more efficient protection from attacks, within the framework of a cyber-risk management provider, shifting the focus to an attacker’s view of a network would be beneficial,” said Bovicelli. “There are obviously limitations in visibility when assessing risk of an external company, but understanding and detecting the services, technologies and opportunities for exploitation criminals look for, is crucial.
“There are many solutions on the market that offer detection and identification of very specific vulnerabilities and services on a company’s external infrastructure, but for an insurance organization scalability is key. This is where CTI can help by focusing detection on specific indicators that significantly increase the risk that the company will be targeted.”
As a CTI expert, Bovicelli has his finger firmly on the pulse of current cyber trends, threat techniques and intrusions. In recent years, the development of RaaS (Ransomware as a Service) has caught his attention.
“The change to a ‘collaborative’ business model has resulted in very efficient anonymous alliances between criminal elements that have proven incredibly difficult to disrupt, even through global law enforcement efforts,” he said. “While a few years ago, the ability to compromise an entire network was limited by the skill-set and expertise of a single attacker or small isolated group, now attackers can lean on the skillset of other groups, work as a decentralized team, even if just for one operation.
“So, if you developed malware that infected a security camera and provided you with only an initial foothold into a company’s network, you can collaborate with a ransomware group with team members and resources needed to turn that access into a full network compromise. We have seen groups seek to hire members with specific skill sets in order to get around a particular security control for a single attack. They also have the budget and operational infrastructure to succeed.”
This has resulted in more coordinated attacks, Bovicelli added, often including several kinds of extortion, from internal documents exfiltration and publishing, threats of DDoS (Distributed Denial of Service) attacks and direct contact with a victim organization’s customers or employees to pressure the company in paying the ransom demand.
“Additionally, the COVID-19 pandemic quickly shifted organizations’ digital footprint and exposure due to the need for more remote access as companies worldwide switched to a ‘work from home’ model,” he said. “More remote access allowed more opportunities for criminal groups to find an entry point into the company’s internal network. The rapid development of multiple federal and state relief programs to aid individuals and businesses during the COVID-19 pandemic period has also been widely exploited by criminals, through both phishing lures and fraud. Overall, these new dynamics resulted in high profitability for cyber criminality.”
Moving forward, Bovicelli urges vigilance. The CTI expert said he doesn’t see the RaaS model disappearing any time soon, and he added that any industry with a high-pressure supply chain, like logistics and shipping, will continue to be targets of ransomware.
“Overall, an insured should always remain vigilant in their cyber security posture and make sure they partner with the right insurance carrier,” he stressed. “As security controls are being developed to address sources of losses and compromise, criminals will continue to develop techniques that circumvent them. Staying ‘ahead of the curve’ by tracking these developments is critical to reducing risk.”
